How to Detect a Phishing Email: Stay One Step Ahead of Cyber Threats
Are you constantly anxious about falling prey to a phishing email? Cybersecurity is a crucial concern, especially concerning sensitive personal information, such as login credentials and credit card details. As a regular email user, understanding how to detect a phishing email is vital for maintaining the security of your digital presence.
This blog will delve into the intricate world of phishing emails and cybersecurity. Utilizing the expertise of BACS Consulting Group, renowned cybersecurity experts in California, we will guide you through identifying phishing emails. This knowledge is not just about securing your inbox; it’s vital to cybersecurity awareness.
A detailed explanation of phishing emails, their common characteristics, and sophisticated techniques like spear phishing will be covered. We will also equip you with practical tips on distinguishing between a legitimate email and a phishing email, supported with real-life examples. Here’s everything you need to know about identifying and protecting yourself from phishing emails.
A Detailed Explanation On Detecting Phishing Emails
Cybercriminals craft phishing emails to seem like they are from a legitimate source. Their primary goal is to trick recipients into revealing sensitive information or clicking on a malicious link. Recognizing a phishing email can be challenging, given the sophisticated methods perpetrators use to make their emails seem authentic. However, there are signs you can look for.
Legitimate Email vs. Phishing Email
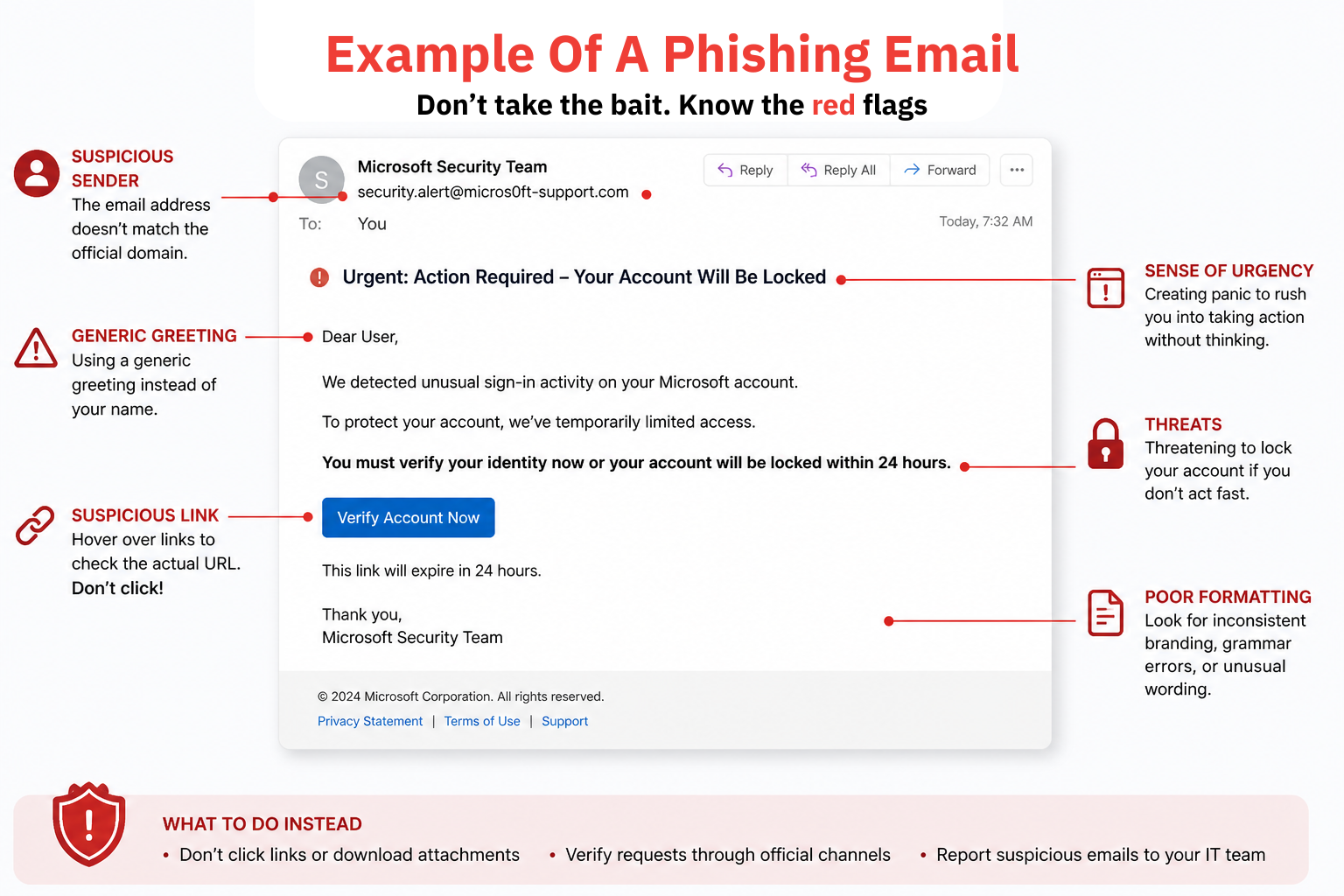
Understanding the subtle differences between legitimate and phishing emails is crucial. While phishing emails often mimic an authentic email’s format, logo, and language, some telltale signs exist. Phishing emails usually instigate a sense of urgency or use fear tactics to compel you into acting quickly, often without thinking. They may also contain generic greetings, typographical errors, or awkward language. Additionally, the email addresses or URLs used in the phishing emails may be slightly altered from the genuine ones.
In contrast, legitimate emails are less likely to demand immediate action or seek sensitive information through email. The language is typically professional and error-free. The email addresses and URLs used consistently align with the organization’s domain.
Phishing Email Examples
Examples of phishing emails can range from fake bank transaction alerts to phony social media notifications. You may receive an email allegedly from your bank notifying you of a suspicious transaction and urging you to log in to confirm. However, the link leads to a fake website that steals your credentials. Similarly, you might get a false notification from a social media platform asking you to click a link and log in to view a post about you. Again, the aim is to harvest your login details.
Spear Phishing: A Targeted Attack
Spear phishing is a more targeted form where the attacker customizes the email to a particular individual, often using information gathered from social media and other public sources. These emails can be harder to detect as they may refer to specific details about you or your work. They often seem to come from a colleague or superior, making the recipient more likely to respond or click a link.
Here’s everything you need to know to protect yourself against phishing threats and elevate your email security.
How to Respond to a Phishing Email
Reacting correctly to a phishing email is essential to maintaining email security. Never reply to the email or click on any links. If the email appears to be from a known source, such as a bank or a colleague, contact them directly through a verified method, not the potentially malicious email. If you mistakenly click on a link, change your passwords immediately and monitor your accounts for unusual activities.
Cybersecurity Training for Phishing Awareness
Consider participating in cybersecurity training to stay one step ahead of phishing threats. Such training programs, like the ones offered by BACS Consulting Group, educate participants about the evolving cyber threat landscape. You will learn how to detect and respond to phishing emails and other cyber threats, thus enhancing your overall phishing awareness.
How to Report Phishing Emails in Microsoft Outlook
Reporting phishing emails helps to prevent others from becoming victims. In Microsoft Outlook, you can report a phishing email by selecting the email, clicking the “Junk” button, and then selecting “Phishing.” The email will be sent to the Anti-Phishing Working Group or your email administrator for review.
The remainder of this article will focus on additional tips to avoid phishing scams, how phishing can impact your online safety, and the importance of regular software updates in phishing prevention.
Additional Tips to Avoid Phishing Scams
In addition to recognizing phishing emails, you should consider other protective measures. Two-factor authentication, for example, provides an extra layer of security by requiring additional verification before access is granted. Always ensure that you use secure and unique passwords for each online account.
The Impact of Phishing on Online Safety
Phishing attacks can severely compromise online safety. A successful phishing attempt can lead to unauthorized access to your accounts, identity theft, financial loss, and more. It can also compromise the security of an entire organization if the victim is part of a business network. Therefore, understanding and implementing effective strategies to detect and prevent phishing attacks is crucial.
The Importance of Regular Software Updates in Phishing Prevention
Keeping your software up-to-date is another essential step in phishing prevention. Updates often include patches for security vulnerabilities that cybercriminals could exploit. So, whether it’s your operating system, browser, or email client, ensure they are continuously updated to the latest version.
The fight against phishing is ongoing, but staying informed and vigilant can significantly reduce your risk. The following section shares some final thoughts and frequently asked questions.
Final Thoughts
Becoming adept at detecting phishing emails is crucial to maintaining your cybersecurity. You’ve taken a significant step towards securing your online presence by understanding the differences between legitimate and phishing emails and recognizing standard phishing techniques such as spear phishing. Through this article, you’ve also learned the importance of reporting phishing emails, the value of cybersecurity training for phishing awareness, and the necessity of regular software updates for phishing prevention.
Stay safe online is not a one-time effort; it requires constant vigilance and an ongoing commitment to learning. However, with the knowledge you’ve gained, you’re well-equipped to tackle the ever-evolving challenges posed by phishing attacks. So, stay alert, stay informed, and most importantly, stay safe.
Let BACS Secure Your Organization Against Phishing Attacks
In the battle against cyber threats, knowledge is your best weapon. While individual vigilance is crucial, an organization’s cybersecurity strategy must be holistic and comprehensive. Organizations must prioritize creating a culture of security awareness, which is where BACS Consulting Group steps in.
As leading cybersecurity experts in California, BACS offers robust cybersecurity training programs tailored to your organization’s unique needs. These programs aim to equip employees at all levels with the knowledge to detect, prevent, and respond to cyber threats, including phishing emails. Through a blend of theory and real-life examples, the training ensures participants gain a practical understanding of how to stay safe in the digital world.
Investing in cybersecurity education and implementing robust security practices with BACS Consulting Group can significantly mitigate the risk of a phishing attack impacting your organization. Remember, a proactive approach is always better than a reactive one in cybersecurity. Secure your organization today for a safer tomorrow.